ICS/OT Business Continuity
Operational Resilience Through Complete OT/IT Separation
Ensure uninterrupted operations with a cyber-hardened architecture that protects your Industrial Control Systems against disruptions, regulatory non-compliance, and costly downtime.
Trusted By Power And Energy Operators Worldwide





24 Countries Globally
Industrial-grade ICS/OT Security
Global Standards Compliance
25+ Years of ICS/OT Service
The Challenge
Business Continuity Risks Are Real - And Costly
Industrial operators face mounting pressures to maintain operations while navigating cyber threats, aging infrastructure, and strict regulatory requirements.

Equipment Obsolescence
DCS, PLCs, and sensors reaching end-of-support create vulnerabilities and procurement nightmares. When legacy components fail, emergency replacements cost 3X more while production halts.
Unplanned Downtime
Industrial facilities lose an average of 27 hours per month to unplanned outages. A single hour can cost millions in lost revenue, contractual penalties, and customer trust erosion.

Asset Management Gaps
Multi-vendor environments create blind spots. Without unified visibility into firmware versions, vulnerabilities, and lifecycle status, you can't protect what you can't see.

Undocumented Procedures
When critical incidents occur without tested procedures, recovery times stretch from minutes to days. Institutional knowledge walks out the door when experienced engineers retire.

Cybersecurity Exposure
2,400 cyberattacks target ICS systems daily. Average incident damage: $5.9M. 47% of breaches threaten human safety. Traditional IT security fails in operational environments..

Compliance & Regulatory Risk
NERC CIP, NIS2, IEC 62443, and NCA ECC-2:2024 demand demonstrable security controls, audit trails, and documented business continuity procedures – or face fines and license risks.
The Solution
ICS Business Continuity Through Complete OT/IT Separation
A cyber-hardened architecture that ensures operational resilience by design – protecting critical systems while enabling secure data flow and regulatory compliance.

Obsolescence Management
Proactive lifecycle tracking and phased replacement planning prevent surprise failures. Transform equipment aging from crisis into controlled transitions aligned with budget cycles.

Standards Compliancee
Built-in audit trails, asset authentication, and network segmentation meet IEC 62443, NERC CIP, NIS2, and NCA ECC-2:2024 requirements – compliance evidence from day one.

Unified Asset Management
Single authoritative view across multi-vendor environments. Track firmware versions, vulnerabilities, and criticality levels – answer compliance questions in minutes, not weeks.
Documented Procedures
Step-by-step playbooks for incident response, recovery, and maintenance. Tested protocols eliminate paralysis during crises and preserve institutional knowledge.

Data Diode Architecture
Hardware-enforced one-way data flow eliminates entire attack categories at the physical level. Malware, unauthorized commands, and reconnaissance physically blocked.

OT-First Cybersecurity
Purpose-built for industrial environments where availability trumps confidentiality. Network segmentation, access controls, and monitoring – without disrupting operations.

Vulnerability Management
Comprehensive risk assessment identifies supply chain threats, unpatched software, and weak authentication. Focus remediation where it matters most to your operations.

Operational Independence
OT systems function independently from IT infrastructure. Enterprise network disruptions, patches, or cyber incidents never halt your critical processes.
Architecture
How Complete OT/IT Separation Works
A layered security architecture that maintains operational continuity while enabling secure data flow and business intelligence.
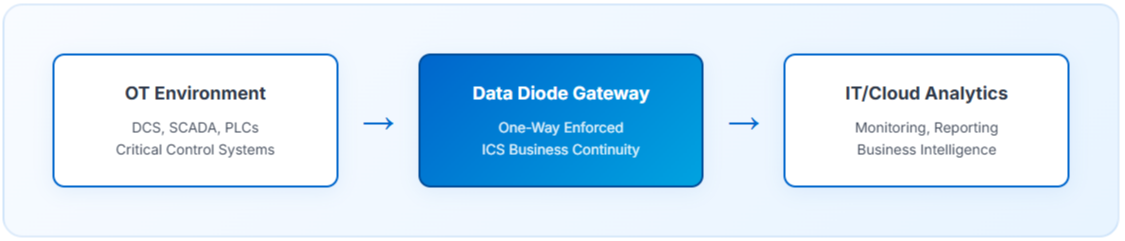

Zero Inbound Threat Vector
Physical impossibility for external systems to send commands or malware back to OT environment.

Independent Operation
OT systems maintain full functionality even during IT infrastructure outages or cyber incidents.

Secure Analytics
Enable predictive maintenance and optimization without compromising operational security or availability.
Audit & Compliance
Complete logging and timestamped records for regulatory reporting and incident investigation.
Regulatory Compliance
Meet Global Standards & Regional Requirements
Comprehensive compliance from day one – designed to satisfy auditors and regulators across jurisdictions.
NERC CIP
- Asset categorization (CIP-002)
- Electronic Security Perimeter
- Multi-factor authentication
- Change & configuration management
- Incident response procedures (CIP-008)
NIS2 & European Standards
- OT security hardening baseline
- Incident notification timelines
- Supply chain risk management
- Vulnerability management
- Business continuity documentation
IEC 62443
- Defense-in-depth architecture
- Network segmentation & zones
- Secure remote access controls
- Security Level certification
- Hardened OS baseline
National Frameworks
- Singapore Cybersecurity Act
- UAE NESA standards
- EMA Grid Code compliance
- ENTSO-E requirements
- Regional TSO specifications
Proven Results
Real-World Business Continuity Success
How a leading power operator achieved operational resilience through complete OT/IT separation
Multi-Site CCGT Power Generation Operator
11+ power stations across 3 continents implementing comprehensive ICS Business Continuity framework.
100%
Operational Uptime
Zero
Cyber Incidents
45 min
Incident Recovery Time
$9M
Downtime Cost Avoided
The Challenge
- Obsolete DCS components with discontinued vendor support
- 72 hours of cascading failures from legacy equipment failure
- Fragmented asset visibility across 5 different vendor tools
- No documented recovery procedures for critical scenarios
- Unpatched vulnerabilities in aging control systems
- Multi-million dollar PPA contract violation penalties at risk
The Solution
- Hardware data diode with physical one-way enforcement
- Unified asset management consolidating 5 vendor silos
- Documented and tested incident response procedures
- Proactive obsolescence tracking and lifecycle planning
- Vulnerability assessment and prioritized remediation
- OT-first network segmentation and access controls
- Full compliance mapping to IEC 62443, NERC CIP, EMA regulations
The Results
- Recovery time reduced from 36 hours to 45 minutes
- Zero unplanned downtime since implementation
- $9M in avoided downtime costs annually
- Vulnerability response time: weeks → minutes
- Eliminated contract violation penalties
Full regulatory compliance with audit-ready documentation - Operational continuity maintained during IT security incidents
Want To Learn More?
Get our free 8-part ICS/OT Business Continuity email series.
Not ready to talk yet?
No problem. We've created a short, 8-email educational series that covers the essential pillars of an ICS/OT Business Continuity framework – the strategy that keeps your systems operational, secure, and compliant, even as threats evolve.
Each email takes less than 3 minutes to read and is designed to give decision-makers, engineers, and consultants a clear understanding of what ICS/OT Business Continuity involves and why it matters.
No jargon. No sales pressure. Just the knowledge that keeps critical infrastructure safe.
✓ 100% free ✓ 100% educational ✓ Unsubscribe anytime
Secure Your Operational Resilience Today
Every company is different, and the state of Industrial Control Systems (ICS) and OT environments varies from company to company making it impossible to present a generic solution that fits every specific situation.
The same goes for how to approach any standards compliance challenges based on your specific situation.
Therefore we'd like to offer you a no-obligations chat about your specific ICS/OT Business Continuity needs and challenges from a current status point of view.
Click the button below, fill out the form, and send it to us, and we'll get back to you shortly.